Our Impact
*Reporting Period 2019 – YTD
Who We Are
Griffiss Institute aims to develop the next generation of STEM talent and defense technologies that will strengthen U.S. national security and create economic opportunity for our region, state and nation.
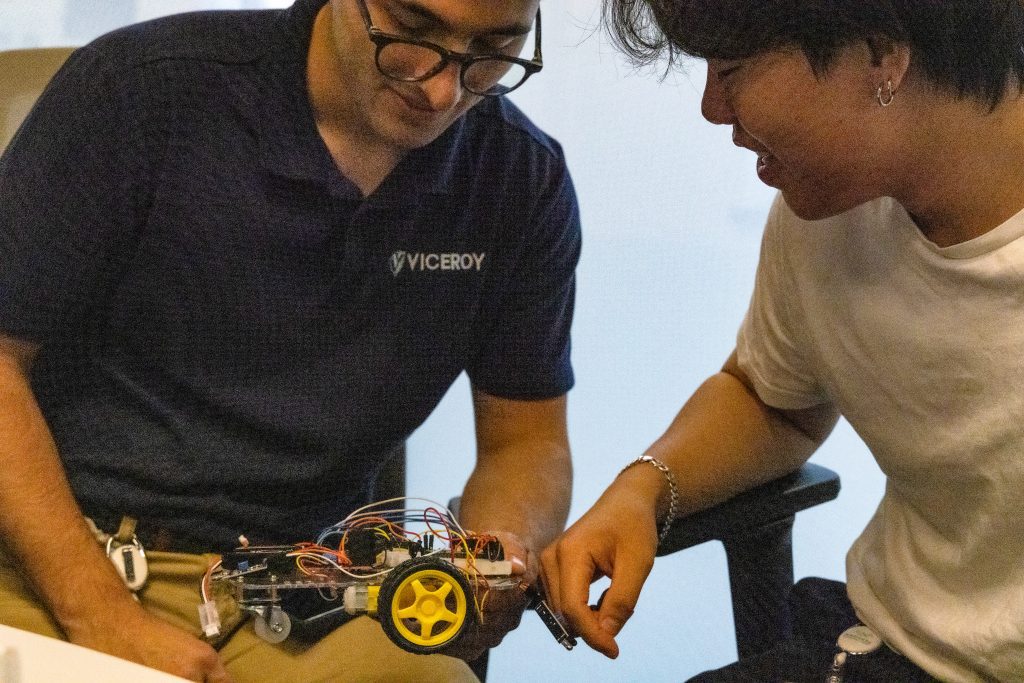
We Elevate TALENT
Griffiss Institute is a nonprofit talent and technology accelerator for the United States Department of Defense (DoD) and an international network of academic, government and industry partners.
We Empower INNOVATION
Since 2002, Griffiss Institute has served the Air Force Research Laboratory Information Directorate (AFRL/RI), the Mohawk Valley region, and the United States, empowering diverse teams with talent and technology development programs that lead the nation in technical and economic impact.
We Enable EXPERIENCE
Devoted to converging teams and technologies to solve complex national challenges, Griffiss Institute is proud to enable its international network from its home at Innovare Advancement Center in New York’s picturesque Mohawk Valley.
Featured Griffiss Institute News:
Congresswoman To Introduce Defense Quantum Acceleration Act
Who We Work With
INDUSTRY
Griffiss Institute facilitates cooperative research and development agreements (CRADAs) with private industry and other federally funded laboratories and commercial test agreements (CTAs) with customers requesting assistance in product validation/verification.





ACADEMIA
We work with universities to collaborate on educational partnership agreements (EPAs) and we provide internship opportunities at various levels. The Air Force Research Lab Information Directorate (AFRL/RI) has previously received the prestigious Federal Laboratory Consortium for Technology Transfer National STEM Award based upon the teaming of the GI and AFRL/RI workforce.

















GOVERNMENT
Griffiss Institute’s dynamic team of professionals is dedicated to making a difference in our nation’s security and defense tech sector through research excellence, a close relationship with AFRL/RI, and our government partners.